Sikov - stock.adobe.com
Enterprise password security guidelines in a nutshell
In this concise guide to passwords, experts at Cyber Tec outline the security problems that put enterprises at risk and offer answers on how to solve them.
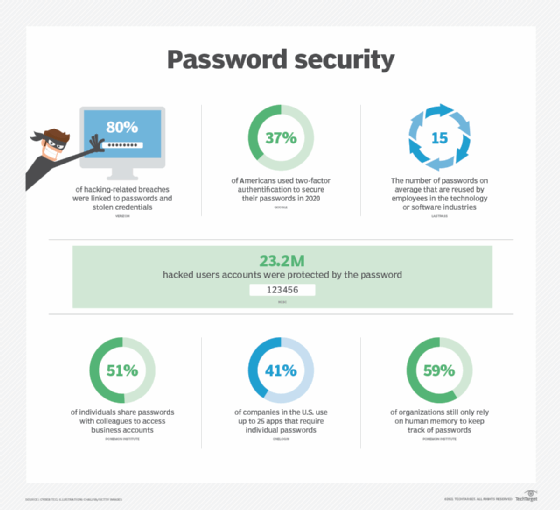
The age-old dilemma of password security continues to haunt businesses both big and small, with poor passwords still a key contributor to data breaches. According to the 2021 Data Breach Investigations Report, in 2019, 80% of hacking-related breaches were reportedly linked to passwords and stolen credentials, showing just how crucial secure password management is within businesses.
Today, many cybercriminals rely on bad password management to successfully hack into an enterprise's networks or systems. Unfortunately, people tend to use simple, memorable passwords across multiple sites, applications and devices. It's no surprise when, according to a late 2019 Harris Poll, 75% of Americans struggle to keep track of all their passwords.
Bad habits make life easier for hackers. Brute-force attacks may be used to guess passwords, even using previous breaches where credentials have been exposed but the user has continued to use the password again elsewhere. Phishing attempts can lead to the extraction of personal information and credentials. Clicking a link or downloading an attachment in a phishing email can deploy certain malware to scan the user's system for credentials or even record user activity and feed it back to the hacker.
This type of risk is concerning for any individual, but matters are made worse when it happens within a business. Without proper management, users continue to practice bad password habits even in a work environment. Yet, one employee's poor password health can lead to a catastrophic cyber attack, exposing sensitive data and allowing access to systems, sometimes going beyond the company and into its supply chain.
Good password security relies on the cooperation of all employees within an organization, but there are things that senior management can and should do to encourage staff to be vigilant and secure.
Create a culture of awareness
Ensuring that employees understand the importance of password security and the risks of weak passwords to a business can help to drive action and get employees to be more thoughtful about security when creating passwords. Many people don't realize the number of ways a hacker can uncover a password, but drawing attention to these techniques and highlighting real-world examples emphasize the need for cyber vigilance. Training sessions and tabletop activities can also be useful for encouraging engagement.
Layer on the password security
Passwords are helpful security tools, but they are so prolific and easy to hack that it doesn't always make sense to use them in isolation. Multifactor authentication (MFA) offers an extra security layer, requiring a second method of authentication, such as a code via text message or approving a sign-on via an authenticator app.
Although MFA can be a little inconvenient, it is key to attack prevention: According to Microsoft, accounts that use MFA are 99.9% less likely to be hacked, which shows just how much of a difference it can make, particularly in high-risk cases.
Use threat detection software
Companies should consider implementing threat detection software, which identifies any suspicious login attempts and alerts your security or IT team. These methods can spot when the second stage of an MFA login has failed, any password spraying attempts or unexpected account lockouts.
Set clear password security guidelines
A company password policy is the best tool for communicating password safety with your employees. Strong password security guidelines provide guidance and instruction on password creation, when to update passwords and other password restrictions. Best practice dictates that passwords should be unique and complex. It's also a good idea to employ password blocklists to avoid common passwords being used that are likely easier to breach. Reading and approving the policy can be included as part of your staff onboarding process, and regular audits to ensure compliance with the policy help keep your company in strong password health.
Always change default passwords
Many new OSes, accounts and software come with pre-installed default passwords that are usually simple and well known. Suffice to say, default passwords are no good if you hope to maintain a secure environment in your organization. Default passwords can be exploited with little effort, giving a hacker access to information or, worse, admin privileges. For proper configuration, all default passwords should be changed, according to your business's password policy.
Employ password managers
A 2020 study by the Ponemon Institute showed that 59% of organizations still only rely on memory to keep track of all their passwords, so you can imagine why employees are likely to choose a password they know they can remember. With the requirements for a strong password becoming increasingly hard to meet, enterprises need to provide appropriate tools, like password managers, to help users keep track of more complex passwords. Password managers can not only help store passwords, but also generate them and auto fill where required, as well as make life more convenient by syncing passwords across multiple devices.
Manage password sharing
When users share passwords, it inevitably introduces more risk, increasing the possibility of a user gaining unauthorized access to data or the password falling into the wrong hands in transit. Sharing passwords via unencrypted messages, as many people do, can lead to them being intercepted by hackers. To reduce risk, password sharing should be avoided, but in the rare cases it has to be done, they should be shared securely -- for example, via an enterprise password management platform. It is also best practice to change a shared password anytime an employee with access to it leaves a company.
Password management may not always feel like a security priority in enterprises, but with so many cyber attacks reliant on stolen credentials, it is a crucial layer of defense and something that every employee needs to have a role in. Passwords could eventually become a thing of the past with passwordless authentication methods becoming more commonplace. But, while passwords are still here, businesses must continue to lay the foundations for good security at the enterprise level by clearly communicating password security guidelines and encouraging cyber vigilance among employees.
Cyber Tec Security is a U.K.-based company focused for over 30 years on promoting cybersecurity for small and medium enterprises. It is one of the U.K.'s leading IASME-qualified cybersecurity Certification Bodies, working to improve the security health of small to medium-sized enterprises through the government's Cyber Essentials certification and its penetration testing products and threat management services. Learn more and check out free resources, including a cybersecurity tip sheet, at CyberTecSecurity.com.