Metasploit 3.1 updates improve Windows penetration testing
Metasploit has long been a popular tool to use to conduct Windows penetration testing. Well, just this January, the latest version, Metasploit 3.1, was released. Learn about the new features and updates of this cool tool, which include a true GUI interface and an increased number of exploits and payloads.
It's here. The latest incarnation of one of my favorite security testing tools -- Metasploit -- is out and ready to roll. Metasploit version 3.1 was officially released in January 2008 and it's the first major upgrade to the exploit framework in almost a year.
The last time I wrote about Metasploit, it had 176 exploits (unique vulnerabilities) and 104 payloads (methods to carry out the exploits). Version 3.1 has 262 exploits and 117 payloads -- many of which are Windows-centric. One of the neat things about Metasploit version 3.1 is that it has a true GUI interface for Windows users. Its new wizard interface opens the tool up to many more potential users. Some people would argue that's a bad thing, but I think the more people supporting the information security cause the merrier.
Creating exploit "jobs" is as simple as stepping through the MSF Assistant, selecting the exploit and payload and then entering some basic information as shown in the following four screenshots.
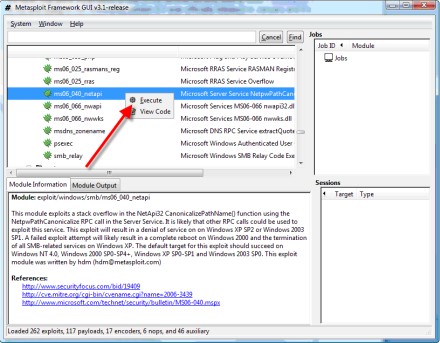
Figure 1 -- Selecting the exploit to carry out.
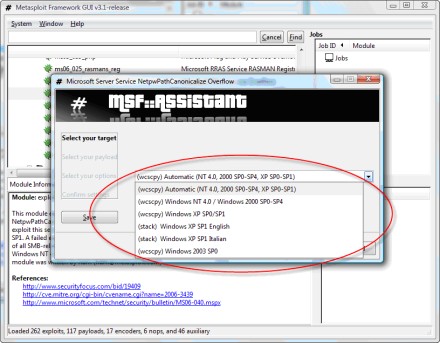
Figure 2 -- Selecting the target host platform.
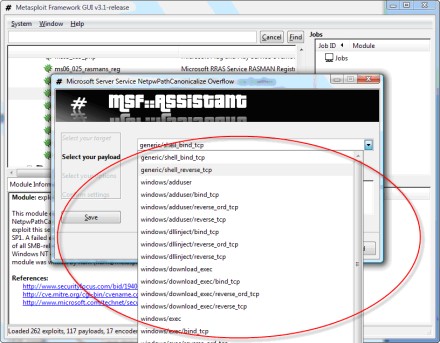
Figure 3 -- Selecting the payload and what to do once the vulnerability is exploited.
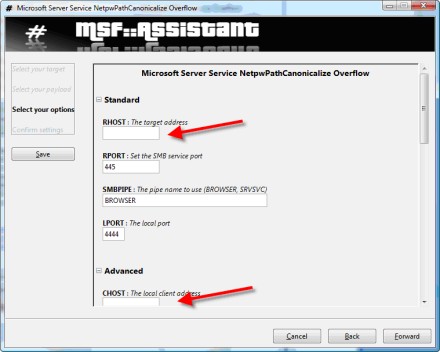
Figure 4 -- Fields to enter some basic host information.
Once you've configured Metasploit and have told it what to do, the job will run and you can see the results in the Module Output window.
If you've been hesitant to try Metasploit in the past due to its command-line complexities in older versions or its awkward browser interface in version 3.0, now's the time to take it for a spin. This new GUI works really well.
One area of confusion for people new to Metasploit is where to begin. How do you actually find the vulnerabilities that Metasploit can 'sploit'? In the context of penetration testing, the best way to go about using it is to find the actual vulnerabilities on your hosts with a scanner such as QualysGuard, LANguard Network Security Scanner or Nessus. Then, once you see what's vulnerable, you can pinpoint your Metasploit attacks and end up with a handy-dandy remote command prompt (a good payload choice) to prove your network has security problems.
If you're not sure which exploits are available for the specific system you're testing or if you want to see, for instance, vulnerabilities for all platforms from a specific year, use Metasploit's search functionality. It's really basic, but it works. A sample search is shown in Figure 5.
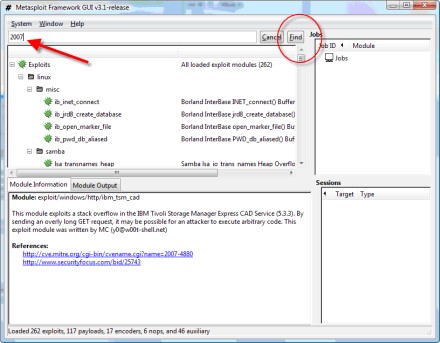
Figure 5 -- Using the search function built into Metasploit 3.1.
So, there you have it. The latest and greatest from HD Moore and company -- Metasploit version 3.1. It might not have the latest exploits like the commercial tools offer, but it's still a fine penetration testing tool. And, unlike many other security testing tools, it really is this simple and it really is free.
ABOUT THE AUTHOR:
Kevin Beaver is an independent information security consultant, keynote speaker and expert witness with Atlanta-based Principle Logic, LLC, where he specializes in performing independent security assessments. He has authored/co-authored several books on information security, including Hacking For Dummies and Hacking Wireless Networks For Dummies (Wiley). He's also the creator of the Security On Wheels information security audio books and blog providing security learning for IT professionals on the go. He can be reached at [email protected].






