Securing removable drives with BitLocker To Go
BitLocker To Go, which ships with Windows 7 Ultimate and Enterprise Editions, can help secure FireWire and USB drives — but is it right for your business?
The new BitLocker To Go can help keep USB and FireWire removable drives from being exploited. However, like the latest incarnation of BitLocker -- which provides decent drive-encryption for individuals and small- and medium-sized businesses but leaves quite a bit to be desired at the enterprise level -- BitLocker To Go has its pitfalls.
BitLocker To Go basics
BitLocker To Go is easy to use. Simply insert a storage device, load up the BitLocker Drive Encryption App in Control Panel and select Turn On BitLocker, as shown in Figure 1.
You'll then be asked if you want to enter a password or use a smart card to protect your drive. A minimum password length is required, ironically, though, it's still possible to enter a ridiculous password like "12345678." (So much for security, huh?) Next, you'll be prompted to save or print the recovery key -- yet another area that can be exploited.
In addition, BitLocker To Go provides portability between Windows 7, Vista and XP systems. Simply install the BitLocker To Go Reader application on your Vista and XP systems. (Note: I've had mixed results with this.)
If you're running one of the above mentioned versions of Windows 7, then perhaps the greatest benefit of BitLocker To Go is that it's built in. I'm a big proponent of using what you've got if it makes sense. Simply enable BitLocker To Go on a removable drive from a Windows 7 system, and you can move it between different Windows systems by entering the password (or smart card) upon insertion.
Note: If you chose the password option, you'll be prompted to "Automatically unlock on this computer from now on." A nicety but arguably a big security weakness waiting to be exploited if both the computer and the removable storage device are lost or stolen.
There are several downsides to BitLocker To Go, including the following:
- There's no support for optical media such as CDs and DVDs.
- There's no support for other operating systems.
- There's no support for writing to BitLocker To Go-protected media on systems that are not running Windows 7 Ultimate or Enterprise (it's read-only).
These annoyances are why third-party vendors such as PGP and WinMagic do so well: They go the extra mile to fill in the Microsoft's gaps, providing the features many enterprises need.
Why should you consider BitLocker To Go?
Regardless of the above mentioned cons, the following are reasons to use BitLocker To Go:
- Removable media are cheap -- often free.
- Most people have some sort of removable storage device at their disposal.
- Employees can use removable media, and you'd probably never know about it.
- You can assume with near-100% certainty that something of business value is going to end up being stored on removable media.
- Removable media are usually unmanaged in all but the most stringent environments, and they typically fall outside the scope of security audits and vulnerability assessments.
And, most importantly:
- It's only a matter of time before removable media containing sensitive information are misplaced, lost or stolen and that sensitive information is put at risk.
The security risk posed by removable media is only going to grow -- and the sky's the limit. With Windows 7 likely being the next viable OS in the enterprise, it's important to take control of this problem.
But only you can know if BitLocker To Go is right for your business. Given the licensing and hidden administrative and compliance costs, BitLocker and BitLocker To Go are by no means "free." However, with today's tight budgets, it certainly wouldn't hurt to look into them.
Overall, if BitLocker isn't a good fit, then BitLocker To Go probably isn't going to be either. If that's the case, third-party vendors will likely have what you need. Regardless, one thing's for sure: The last thing you need is multiple mobile encryption systems to manage because system complexity is one of security's biggest enemies. Therefore, it doesn't necessarily matter the path you choose to go down -- just do something.
ABOUT THE AUTHOR:
Kevin Beaver is an information security consultant, expert witness, author and professional speaker at Atlanta-based Principle Logic LLC. With over 22 years of experience in the industry, he specializes in performing independent security assessments around information risk management. He has authored/co-authored 10 books on information security including the best-selling Hacking For Dummies. In addition, he's the creator of the Security On Wheels information security audio books and blog providing security learning for IT professionals on the go. You can reach him through his website www.principlelogic.com, follow him on Twitter at @kevinbeaverand connect to him on LinkedIn.

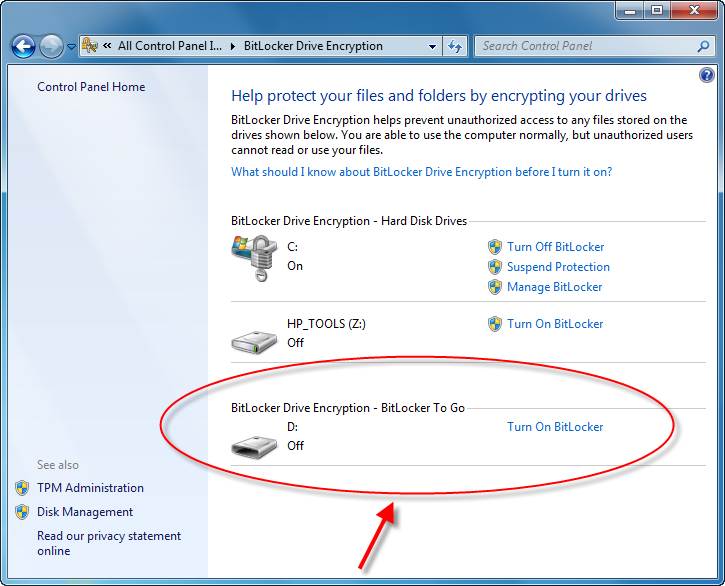 Figure 1: Enabling BitLocker in Windows 7 Control Panel (Click to enlarge)
Figure 1: Enabling BitLocker in Windows 7 Control Panel (Click to enlarge)




