Security Accounts Manager
What is the Security Accounts Manager (SAM)?
The Security Accounts Manager (SAM) is a database file in the Microsoft Windows operating system (OS) that contains usernames and passwords.
The primary purpose of the SAM is to make the system more secure and protect from a data breach in case the system is stolen. The SAM is available in different versions of Windows, including Windows XP, Windows Vista, Windows 7, Windows 8.1, Windows 10 and the Windows 11.
What does the Security Accounts Manager do?
Each user account can be assigned a local area network (LAN) password and a Microsoft Windows password in the SAM. For increasing security, both of these are encrypted and cannot be accessed by any user. These are also referred to as password hashes. In simple terms, think of it as a locked diary with all a user's passwords.
During a user's login attempt, the Windows system will ask for a username and password. Once the password is entered, it will be verified against the password in the SAM. If the username and associated passwords match an entry in the SAM, a sequence of events will take place. This will ultimately result in granting the user access to the system.
On the other hand, if the username and passwords do not match any entry in the SAM, it will return an error message. The user will be requested to enter the information again.
If the personal computer (PC) is used by only one user, and the PC is not connected to LAN, the SAM will only store and ask for one user's password. Once the system is accessed, the SAM file continues to run in the background.
What is the purpose of the Security Accounts Manager?
The primary purpose of the SAM in a PC environment is to make it difficult for a thief to access the data on a stolen machine. It can also provide some measure of security against online hackers.
If the user does not care for such security, they can disable this function to access the system without inputting the password. In such a case, the user will not be asked to enter authentication data every time the computer is switched on or restarted.
Can a user access the Security Accounts Manager?
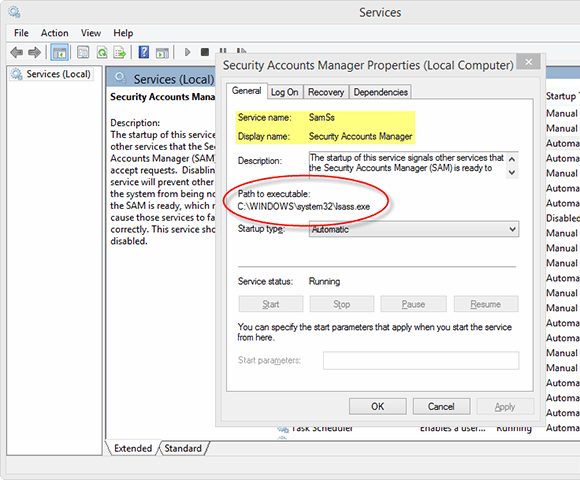
SAM is part of the registry and can be found in the C Drive on the hard disk. This means that the SAM data is locally stored.
Due to this, it is used in the case of a local logon. The user will only be able to access the data which is stored in that profile. However, domain user logon attempts are handled by the Active Directory (AD). Similarly, a Windows server with a domain controller (DC) will also access login data from the AD.
The SAM database file is stored within C:\Windows\System32\config. All of the data within the file is encrypted. The passwords hashes are stored in HKEY_LOCAL_MACHINE\SAM. As the primary purpose of the SAM is to increase security, its access is restricted.
Even though it is stored locally, any system user cannot access the file while running. For security reasons, different permissions govern access to the SAM. HKLM/SAM and SYSTEM privileges are required for accessing it. For added security, Windows introduced the Syskey function in Windows NT 4.0. This can be activated using the Syskey program.
See also: Construct a solid Active Directory password policy, Incorporating zero trust into endpoint security, A closer look at new and updated Microsoft security features and How to enable and disable Tamper Protection in Windows 10.