General Data Protection Regulation (GDPR)
What is the General Data Protection Regulation (GDPR)?
The General Data Protection Regulation (GDPR) is legislation that updated and unified data privacy laws across the European Union (EU). The GDPR was approved by the European Parliament on April 14, 2016, and went into effect on May 25, 2018.
It replaces the EU Data Protection Directive of 1995. The new directive focuses on keeping businesses more transparent and expanding the privacy rights of data subjects. When an organization detects a serious data breach, it's required by the GDPR to notify all affected people and the supervising authority within 72 hours. Mandates in the GDPR apply to all data produced by EU citizens, regardless of whether the company collecting the data in question is located within the EU, as well as all people whose data is stored within the EU, regardless of whether they're EU citizens. The GDPR also defines penalties for noncompliance.
What is the purpose of GDPR?
The purpose of the GDPR is to protect individuals and the data that describes them and to ensure the organizations that collect that data do so in a responsible manner. The GDPR also mandates that personal data is maintained safely; in part, the regulation says personal data must be protected against "unauthorized or unlawful processing, and against accidental loss, destruction or damage."
Reasons for collecting personal data are also defined in the GDPR; the data that's collected must be for a specific and legitimate purpose and shouldn't be used in any way beyond that intention. The regulation also suggests limits on how much data is collected, saying that data collection should be "limited to what is necessary in relation to the purposes for which they are processed." The GDPR further states that the organization collecting data should ensure it's accurate and updated as necessary.
This article is part of
What is data protection and why is it important?
Under the GDPR, companies can't legally process any person's personally identifiable information (PII) without meeting at least one of the following six conditions:
- Express consent of the data subject.
- Processing is necessary for the performance of a contract with the data subject or to take steps to enter a contract.
- Processing is necessary for compliance with a legal obligation.
- Processing is necessary to protect the vital interests of a data subject or another person.
- Processing is necessary for the performance of a task carried out in the public interest or the exercise of official authority vested in the controller.
- Processing is necessary for legitimate interests pursued by the controller or a third party, except where such interests are overridden by the interests, rights or freedoms of the data subject.
In addition, companies that conduct data processing or monitor data subjects on a large scale must appoint a data protection officer (DPO). The DPO is the figurehead responsible for data governance and ensuring the company complies with GDRP. If a company doesn't comply with the GDPR, legal consequences can include fines of up to 20 million euros ($21.77 million USD) or 4% of annual global turnover. In addition, the person in this role is responsible for ensuring appropriate data protection principles are applied to the maintenance of personal data.
History of GDPR
The roots of the EU's GDPR can be traced back to the 1950 EU Convention on Human Rights, which laid out basic human rights that member states must respect.
As computers became more ubiquitous in the business and governmental spheres, additional regulations were put in place, such as the 1981 Data Protection Convention, which declared privacy a legal right.
The European Data Protection Directive that was enacted in 1995 is most closely related to the GDPR and is seen as that regulation's forerunner.
What data does GDPR protect?
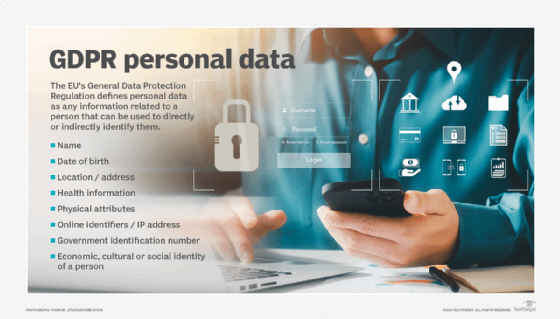
Users must give consent to any company or organization that wishes to collect and use personal data. As defined by the GDPR, personal data is information that relates to "an identified or identifiable natural person" -- referred to as a data subject.
Personal data includes the following types of information:
- Name.
- Identification number.
- Location data.
- Any information that is specific to "the physical, physiological, genetic, mental, economic, cultural or social identity of that natural person."
- Biometric data that's acquired through some form of technical process, such as facial imaging or fingerprinting.
- Information related to a person's health or healthcare.
- Racial or ethnic information of an individual.
- Political opinions or religious beliefs.
- Union membership.
What are the 7 principles of GDPR?
The GDPR lays out the following seven basic principles on which it bases its regulations and rules of compliance related to personal data:
- Lawfulness, fairness and transparency. The data subject must be clearly informed about how their data will be used.
- Purpose limitation. Data can be collected only for specific purposes.
- Data minimization. The amount of data collected is limited to what is necessary for specific processing.
- Accuracy. Organizations collecting data must ensure its accuracy and update it as necessary. Data must be deleted or changed when a data subject makes such a request.
- Storage limitation. Collected data won't be retained longer than needed.
- Integrity and confidentiality. Appropriate protection measures must be applied to personal data to ensure it's secure and protected against theft or unauthorized use.
- Accountability. Data collectors are responsible for ensuring compliance with the GDPR.
The seven principles of the GDPR underlie specific data subject rights, including the following:
- Right to be forgotten. Data subjects can request PII to be erased from a company's storage. The company has the right to refuse requests if it can successfully demonstrate a legal basis for their refusal.
- Right of access. Data subjects can review the data an organization has stored about them.
- Right to object. Data subjects can refuse permission for a company to use or process their personal data. The company can ignore the refusal if it can satisfy one of the legal conditions for processing the subject's personal data but must notify the subject and explain the reasoning behind doing so.
- Right to rectification. Data subjects can expect inaccurate personal information to be corrected.
- Right of portability. Data subjects can access the personal data a company has about them and transfer it.
Who is subject to GDPR compliance?
All organizations that collect personal data of any citizen of an EU member state must comply with the GDPR. That includes organizations that reside outside the EU -- they still must comply with the GDPR if they're collecting a member state citizen's personal data.
The regulations apply regardless of the method used to collect personal data; this includes data collected by methods other than websites and other internet tools. The GDPR defines the three roles related to personal data as follows:
- Data subject. Owner of personal data.
- Data controller. The individual or organization determining what personal data to collect and how it will be used.
- Data processors. The individual or organization processing personal data for the controller.
Breach notifications
In the event of a security breach that affects stored personal data, the data controller must notify the supervisory authority within 72 hours of the breach. The supervisory authority is defined as the public authority that has been designated by the EU member country to oversee GDPR compliance.
Additional requirements relevant to breach notifications include the following:
- If notification isn't made within the allocated 72 hours, the data controller must provide the reason for the delay.
- Breach notifications must include, at minimum, the nature of the breach, the number and types of data subjects' personal data that could be compromised and the number of data records that could be involved.
- The data-controlling organization must also describe any possible consequences resulting from the breach and describe what measures will be taken to mitigate the effects.
- Notification of the data breach must be delivered directly to the victims, not in the form of a general announcement.
- The data controller must document the breach and the remedies it has applied, as well as provide the documentation to the supervisory authority for verification.
Fines and penalties for noncompliance
Penalties for noncompliance or data breaches can be severe. Several criteria are assessed to determine appropriate penalties, including the severity of the breach, the breach's duration, the number of data subjects affected by the breach and the degree of damage that the breach incurred.
Other factors that might influence penalties include the following:
- If a data breach was caused by negligence or intentional.
- Failure to keep adequate records of personal data collection and processing; fines can be as much as 10 million euros or 2% of annual revenues.
- Not complying with any orders handed down by supervisory authorities; these fines can be up to 20 million euros or up to 4 % of the total revenues.
Although the GDPR has been in effect for only a few years, some significant fines have been levied to date by data protection authorities in Europe, in particular, such as the following:
- TikTok. In September 2023, the Irish Data Protection Commissioner imposed a fine of €345 million on the social media giant for GDPR violations centering on its handling of children's accounts.
- Meta. In May 2023, the Irish Data Protection Commission imposed a fine of €1.2 billion.
- Google LLC. In December 2021, the French Data Protection Authority imposed a fine of €90 million on Google for its inability to allow YouTube users in France to refuse cookies as easily as they could accept them.
- WhatsApp. In September 2021, the Irish Data Protection Commission imposed a fine of €225 million on WhatsApp for transparency infringements.
- Amazon. In July 2021, the Luxembourg National Commission for Data Protection imposed a fine of €746 million.
GDPR and third-party data
There are several regulations regarding personal data obtained from parties other than the data subjects and related to sharing of personal data outside the EU.
- A data controller must obtain permission to transfer data to another country or international organization.
- If personal data is collected from other sources than the data subject, the data controller must provide a description of the data and its origin to the data subject.
Some critics expressed concern about the United Kingdom's withdrawal from the EU regarding the effect on the country's compliance with the GDPR. The U.K. has updated its Data Protection Act 1998 with a new law called the Data Protection Act 2018. The new law hews closely to the rules defined in the GDPR, but U.K. companies that do business with customers or other organizations in EU member states are expected to comply with the GDPR.
6 steps to ensure GDPR compliance
The GDPR describes the expected results of good and responsible data management, but it doesn't define any specific technical measures for data collectors must use to meet that goal.
Some best practices to help ensure compliance with the GDPR include the following:
- Always ask before collecting personal data; data subjects must be willing participants.
- Only collect what you really need; organizations will be responsible for all the data they collect, regardless of whether they use it.
- Don't share data with other entities, unless users have agreed, and supervisory authorities have approved the transaction.
- Encrypt all personal data -- both at rest and in flight.
- Ensure at least two up-to-date and secure backup copies of all personal data are maintained at two separate off-site locations.
- Have the tools to easily edit or delete specific items of personal data and to verify and document the actions.
Responsible data management also extends to protecting your credit card information. Learn how cybercriminals steal credit card information and how you can protect yourself from being exploited.