How to create an internal phishing campaign from scratch
When IT begins an email phishing campaign, it must determine what server the emails will come from, consider phishing tool options and more.
A phishing test is arguably one of the most valuable security assessments you can perform as an IT professional.
Phishing security isn't like other types of security where you can invest in a service or software to prevent attacks because users play such a critical role. The best way to address this security concern is to execute an internal phishing campaign in which you phish your own users to understand which users are most vulnerable to such attacks.
With all the risks associated with phishing attacks, including stealing login credentials, malware infections and the exploitation of information assets, phishing security is too important to overlook. Creating an internal phishing campaign is crucial, and it doesn't have to be difficult.
Set up a phishing server
To start an internal phishing campaign, you need an email client and a server to send your messages through. You can create your own server and send out emails that look like they originated from your own email system, a similar domain, or a third-party email or cloud-based service that most users are familiar with.
The server setup process can take a while to fine-tune, and the server only provides rudimentary capabilities to report and measure progress. A small server is not scalable for an entire enterprise security program. A separate, small-scale server is perfect for an internal phishing campaign, however, as long as you don't expect it to do any more than that.
Phishing campaign tools
Free phishing tools provide some value at no cost, but you can get a lot more out of paid phishing products and services. Companies such as KnowBe4 and Cofense are common tools you can use for an internal phishing campaign.
You could also choose a lesser-known but viable phishing and awareness platform called Lucy. There are numerous ways to try and exploit your users and endpoints with the Lucy phishing templates.
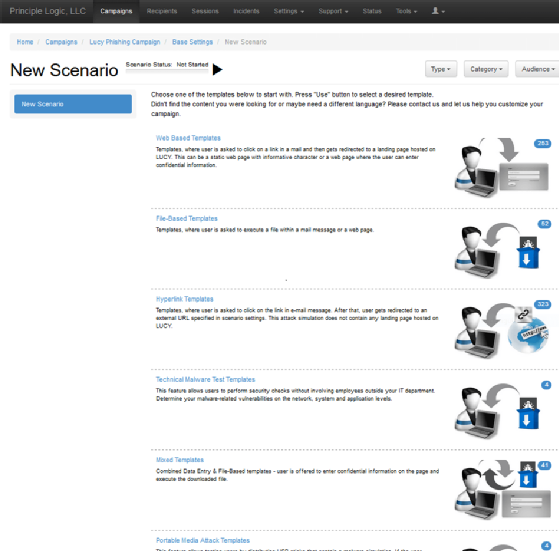
You can run malware simulations, SMS phishing and perform a risk assessment that uses attack scenarios based on your industry type. Lucy and many other phishing tools provide awareness training that is the most valuable, yet most overlooked, aspect of an internal phishing campaign.
Design the campaign
Regardless of which tool you use, there are two main steps that make up an internal phishing campaign.
First, you must decide whether you want to mimic your own organization's email domain or use a similar domain that's made up of misspellings or other differentiators, such as adding the suffix tech to the end of your domain -- [email protected]. A similar domain name includes indicators that your users should pick up on once they receive the email.
Once you choose the domain, you must come up with a compelling message to lure users into doing something they shouldn't do, such as clicking a link, downloading and opening an attachment, or providing login credentials. Messages that look like they're coming from a manager or executive within the organization requesting that users do something within a certain time frame are typically successful.
Dear Colleague:
As part of our nationaly-certified Women's Business Enterprise initiatives, we need to solicit your feedback to the exec committee about the busines and how it operates. Please visit this link to the survey here today to let us know what you think.
Regards,
Chris Smith, SHRM-SCP -- HR Director
This urgent email from a business director that affects people personally is an excellent example of an email in an internal phishing campaign. Your users will often follow the instructions without thinking about what they're doing. The next thing you know, they've submitted their network login credentials or other sensitive information that the email prompted them for.
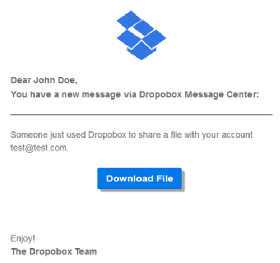
Another approach is to notify your users that they have a file ready for download from one of the popular cloud-based file sharing services, such as Dropbox.
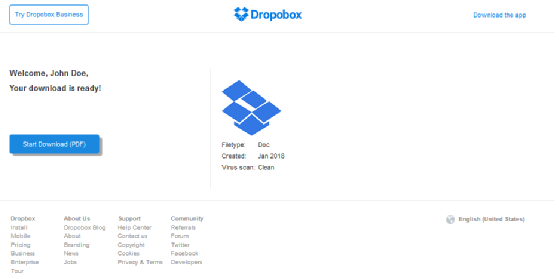
Once the user takes the specific action you're soliciting, you can end the internal phishing campaign or redirect them to an awareness website so they can learn more about the choices they made.
Make the incident a teachable moment, but do so in a way that's not demeaning. Getting management or your security committee involved is critical because it demonstrates that phishing security is an organization-wide issue rather than just a criticism from IT.







